To create and configure a Virtual Cloud Network (VCN) named IAD-SP-PBT-VCN-01 with an Internet Gateway and appropriate route rules for external connectivity, follow these steps based on the Oracle Cloud Infrastructure (OCI) Networking documentation.
Step-by-Step Solution for Task 3: Create and Configure a VCN and Private Subnet
Log in to the OCI Console:
Use your OCI credentials to log in to the OCI Console (https://console.us-ashburn-1.oraclecloud.com).
Ensure you have access to the assigned compartment.
Navigate to Virtual Cloud Networks:
From the OCI Console, click the navigation menu (hamburger icon) on the top left.
Under Networking, select Virtual Cloud Networks.
Create a New VCN:
Click Start VCN Wizard and select Create VCN with Internet Connectivity.
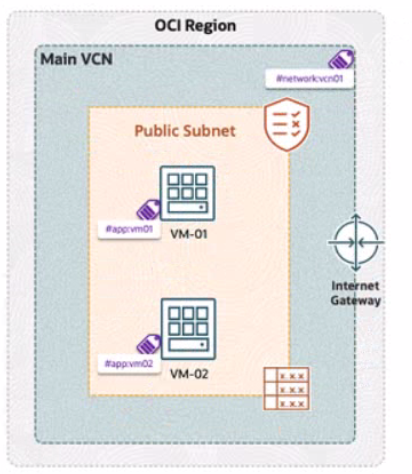
VCN Name: Enter IAD-SP-PBT-VCN-01.
Compartment: Select the assigned compartment.
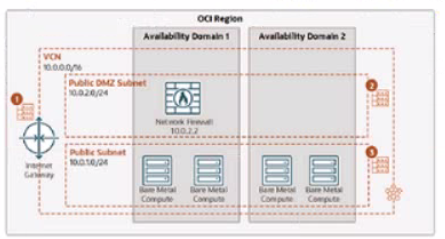
VCN CIDR Block: Enter 10.0.0.0/16 (matches the diagram's VCN CIDR).
Public Subnet CIDR Block: Enter 10.0.10.0/24 (matches the diagram's public subnet).
Accept the default settings for the public subnet and Internet Gateway creation.
Click Create to provision the VCN, Internet Gateway, and public subnet.
Verify the Internet Gateway:
After creation, go to the VCN details page for IAD-SP-PBT-VCN-01.
Under Resources, select Internet Gateways.
Ensure the Internet Gateway is attached and enabled.
Configure Route Rules:
In the VCN details page, under Resources, select Route Tables.
Select the default route table associated with the public subnet (10.0.10.0/24).
Click Add Route Rules.
Target Type: Select Internet Gateway.
Destination CIDR Block: Enter 0.0.0.0/0.
Target Internet Gateway: Select the Internet Gateway created with the VCN.
Click Add Route Rule to save.
Update Security List (if needed):
Under Resources, select Security Lists.
Edit the default security list for the public subnet.
Add an ingress rule:
Source CIDR: 0.0.0.0/0
IP Protocol: TCP
Source Port Range: All
Destination Port Range: 22 (for SSH) or as required by your application.
Add an egress rule:
Destination CIDR: 0.0.0.0/0
IP Protocol: All
Save the changes.
Note the VCN OCID:
Return to the VCN details page for IAD-SP-PBT-VCN-01.
Copy the OCID displayed (e.g., ocid1.vcn.oc1..<unique_string>).
OCID of the Created VCN
Enter the OCID of the created VCN (IAD-SP-PBT-VCN-01) into the text box. The exact OCID will be available after Step 3 (e.g., ocid1.vcn.oc1..<unique_string>).