Comprehensive Detailed Step-by-Step Explanation with All Juniper Security Reference:
Understanding SRX Packet Flow:
The SRX Series device processes traffic in a specific sequence of operations, including zones, security policies, NAT, and services.
UTM (Unified Threat Management) features, such as antivirus, web filtering, and content filtering, are considered advanced services and are applied during the services processing stage.
Explanation of Each Option:
Option A: Services
UTM features are categorized under 'services' because they involve advanced traffic inspection, filtering, and threat detection.
UTM services are triggered after basic security policies are applied and are performed as part of the packet processing workflow.
Correct.
Option B: Security Policies
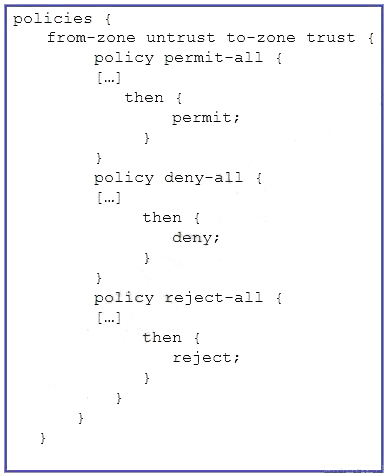
Security policies are used to allow, deny, or permit traffic between zones.
Although policies determine whether traffic is allowed, UTM services are applied only after traffic matches a security policy that permits it.
UTM processing does not occur during the security policies stage.
Incorrect.
Option C: Zones
Zones define the logical segmentation of a network on SRX devices.
While zones determine traffic directionality and security boundaries, UTM features are not applied at this stage.
Incorrect.
Option D: Screens
Screens are used for DoS (Denial of Service) protection and detect specific types of malicious activity, such as SYN floods or port scans.
Screens focus on session-level protections, not UTM-specific traffic filtering or inspection.
Incorrect.
Where UTM Fits in the Packet Flow:
After a security policy permits traffic, advanced features such as UTM are applied in the services processing stage.
The typical SRX packet flow includes:
Ingress Interface
Zones and Screens
Security Policies
Services (UTM, IDP, etc.)
NAT (if applicable)
Egress Interface
Juniper Security Reference:
Refer to the Juniper SRX Packet Flow Documentation for more details on how UTM and services are integrated into the packet flow.