SCENARIO
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephone, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q's business model, resources are contracted as needed instead of permanently employed.
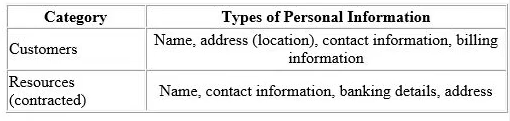
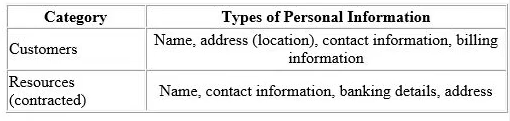
The table below indicates some of the personal information Clean-Q requires as part of its business operations:
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation. Therefore, the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q's traditional supply and demand system that has caused some overlapping bookings.
Ina business strategy session held by senior management recently, Clear-Q invited vendors to present potential solutions to their current operational issues. These vendors included Application developers and Cloud-Q's solution providers, presenting their proposed solutions and platforms.
The Managing Director opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform: A web interface that Clean-Q accesses for the purposes of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customers to pay for services.
Which question would you most likely ask to gain more insight about LeadOps and provide practical privacy recommendations?
Show Answer
Hide Answer
Correct Answer:
C
To gain more insight about LeadOps and provide practical privacy recommendations, asking where LeadOps' operations and hosting services are located is essential.
Data Residency and Sovereignty: The physical location of data processing and storage facilities impacts compliance with data protection laws. Different countries have different regulations concerning data privacy and security.
Jurisdictional Issues: Knowing the location helps assess the legal jurisdiction governing the data. This includes understanding any potential requirements for data transfer, local laws, and the legal obligations LeadOps must comply with.
Cross-Border Data Transfers: If data is hosted in a different country, Clean-Q must ensure that adequate safeguards are in place for cross-border data transfers. This is particularly relevant under GDPR, which requires appropriate data transfer mechanisms like Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs).
Risk Assessment: The geopolitical stability and data protection framework of the hosting location can influence the security and privacy risks associated with using LeadOps.
IAPP Privacy Management, Information Privacy Technologist Certification Textbooks
GDPR Chapter V -- Transfers of Personal Data to Third Countries or International Organizations
NIST SP 800-37: Guide for Applying the Risk Management Framework to Federal Information Systems