Refer to the scenario.
This customer is enforcing 802.1X on AOS-CX switches to Aruba ClearPass Policy Manager (CPPM). The customer wants switches to download role settings from CPPM. The ''reception-domain'' role must have these settings:
--- Assigns clients to VLAN 14 on switch 1, VLAN 24 on switch 2, and so on.
--- Filters client traffic as follows:
--- Clients are permitted full access to 10.1.5.0/24 and the Internet
--- Clients are denied access to 10.1.0.0/16
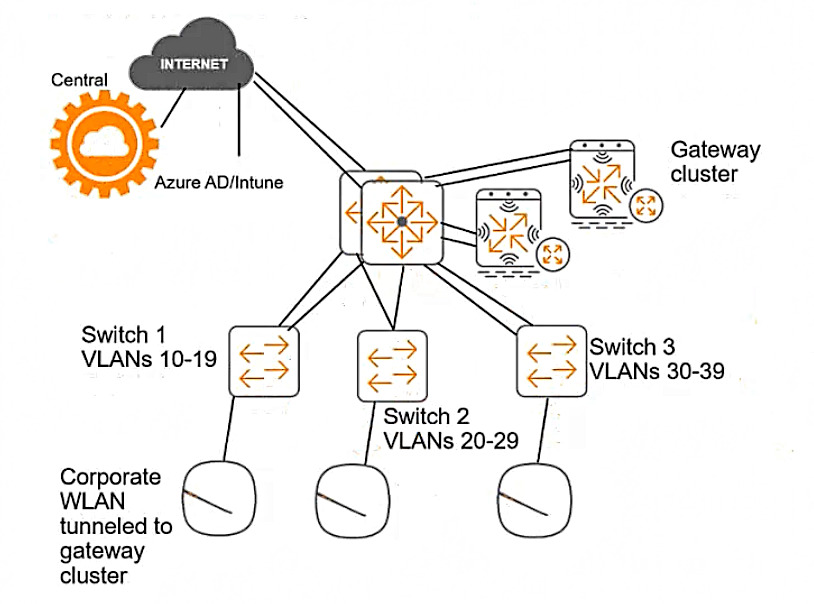
The switch topology is shown here:
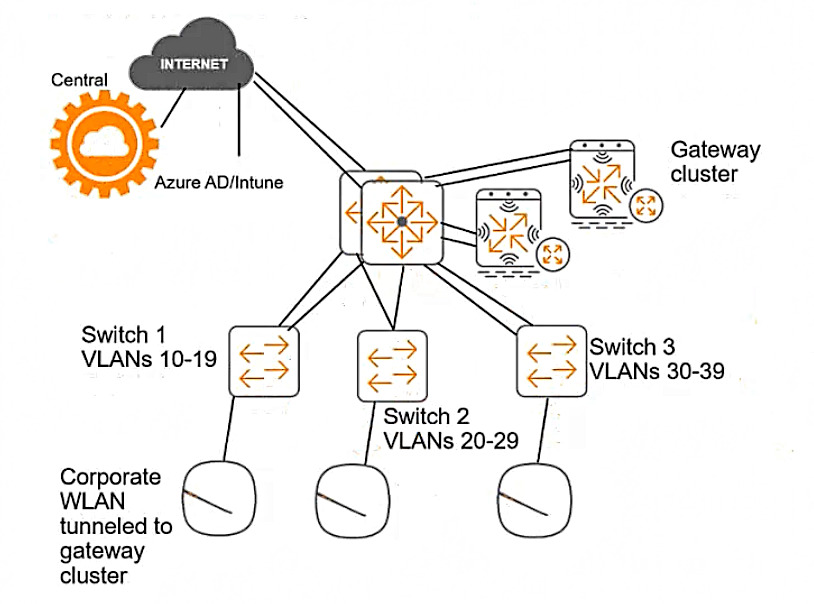
How should you configure the VLAN setting for the reception role?
Show Answer
Hide Answer
Correct Answer:
A
According to the AOS-CX User Guide, one way to configure the VLAN setting for the reception role is to assign a consistent name to VLAN 14, 24, or 34 on each access layer switch and reference that name in the enforcement profile VLAN settings. This way, the switches can download the role settings from CPPM and apply the correct VLAN based on the name, rather than the ID. For example, the enforcement profile VLAN settings could be:

And the VLAN configuration on each switch could be: