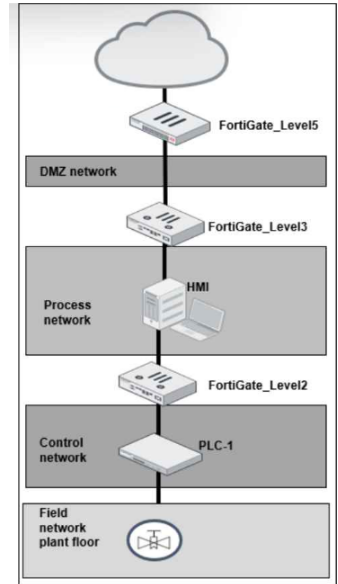
Refer to the exhibit.
A simplified OT network is shown. You want to optimize the protection of this OT network. Which two controls must you implement? (Choose two answers)
Correct Answer:
B, C
The correct answers are B. IPS on FortiGate_Level5 and C. Virtual patching on FortiGate_Level2.
The study guide explains that ''the first line of defense is securing the IT side of your network'' and that FortiGate should be placed to protect ICS environments and stop threats from propagating from IT into OT. It also states that IPS improves OT security because ''today's threat landscape requires IPS to block a wider range of threats and improve OT security'' and that in IPS mode, vulnerable devices are protected. This makes FortiGate_Level5, at the upper boundary near the DMZ and external connectivity, the correct place to implement IPS as a primary protection control.
The study guide also states in the Purdue model section that ''Level 2 consists of the processes and programs that control the PLCs, RTUs, and IEDs found at Level 1'' and that ''it is necessary to segment, or even microsegment, these servers with firewall segmentation, along with policies that include application control and virtual patching.'' In addition, the virtual patching section says ''Virtual patching protects OT devices that have not yet been updated against vulnerability exploits'' and applies when traffic related to the vulnerable device reaches the firewall policy. Since FortiGate_Level2 sits between the process network and the control network, it is the right enforcement point for virtual patching to protect the PLC-side assets.
Option A is not one of the best answers because offline IDS only detects and logs attacks; the guide says ''no traffic flows through FortiGate'' in offline IDS mode, whereas IPS can actually block threats. Option D is also not the best answer because OT signatures are enabled within the IPS framework, but the stronger control explicitly described for this design is to deploy IPS at the upper boundary and virtual patching closer to vulnerable OT devices.