A user was attempting to register their host through the registration captive portal. After successfully registering, the host remained in the registration VLAN. Which two conditions would cause this behavior? (Choose two.)
Correct Answer:
C, D
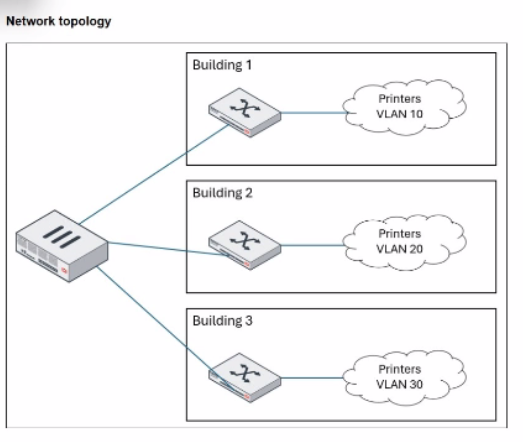
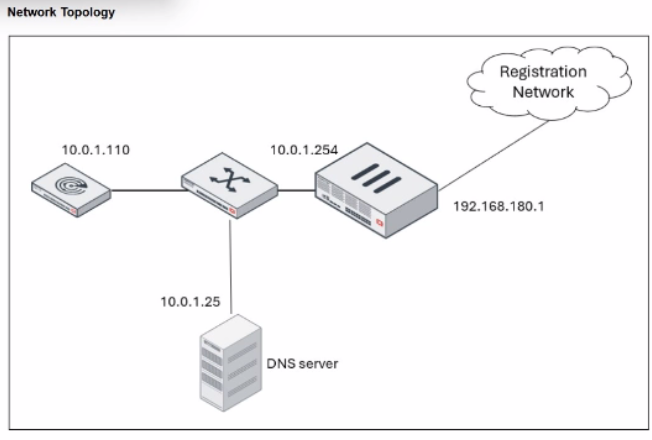
The process of moving a host from a Registration VLAN to a Production VLAN (Access VLAN) is a fundamental part of the FortiNAC-F 'VLAN steering' workflow. When a host successfully registers via the captive portal, FortiNAC-F evaluates its Network Access Policies to determine the correct VLAN. If the host remains stuck in the Registration VLAN despite a successful registration, it is typically due to port-level restrictions or the presence of other unregistered devices.
The two most common reasons for this behavior as per the documentation are:
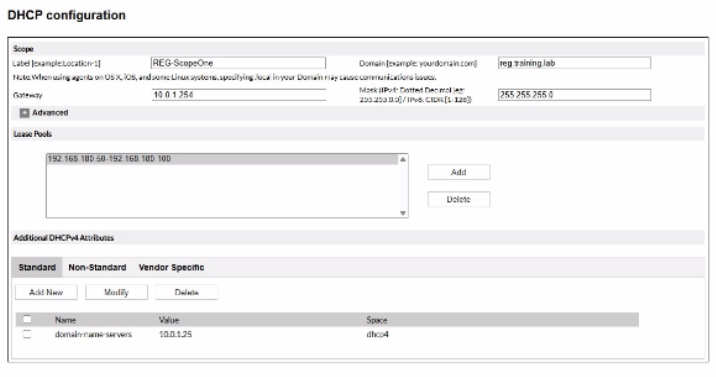
The port default VLAN is the same as the Registration VLAN: If the 'Default VLAN' field in the switch port's model configuration is set to the same ID as the Registration VLAN, the port will not change state because FortiNAC-F believes it is already in its 'normal' or 'forced' state.
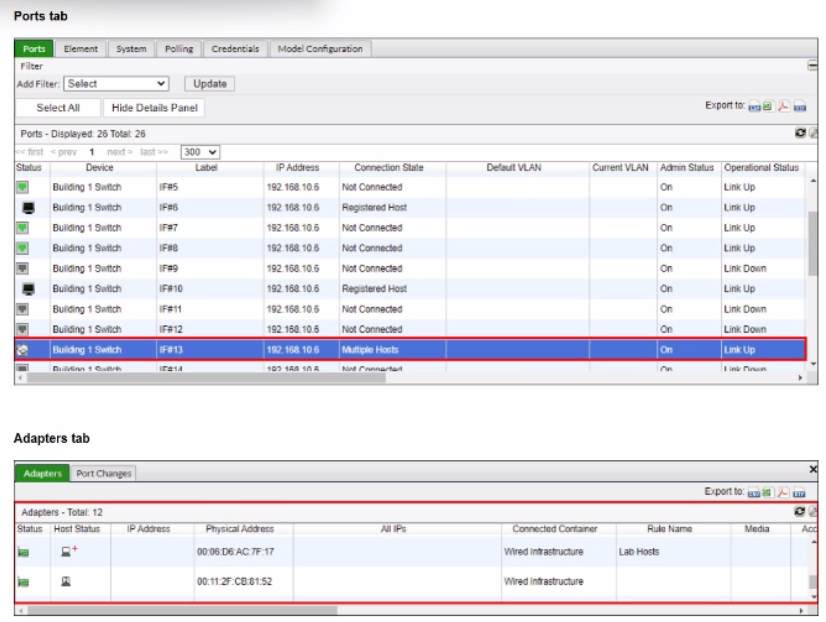
There is another unregistered host on the same port: FortiNAC-F maintains the security posture of the physical port. If multiple hosts are connected to a single port (e.g., via a hub or unmanaged switch) and at least one host remains 'Rogue' (unregistered), FortiNAC-F will generally keep the entire port in the isolation/registration VLAN to prevent the unregistered host from gaining unauthorized access to the production network.
Issues with agents (A, B) typically prevent a host from completing compliance or registration but do not usually result in a 'stuck' status after registration has already been marked as successful in the system.
'If a port is identified as having Multiple Hosts, and those hosts require different levels of access, FortiNAC remains in the most restrictive state (Registration or Isolation) until all hosts on that port are authorized... Additionally, verify the Default VLAN setting for the port; if the Default VLAN and Registration VLAN match, the system will not trigger a VLAN change upon registration.' --- FortiNAC-F Administration Guide: Troubleshooting Host Management.