Comprehensive and Detailed Explanation From Exact Extract of Forescout Platform Administration and Deployment:
According to theForescout Administration Guide and RADIUS Plugin Configuration Guide, the best practice for ordering sub-rules is that thefirst rule should capture the lowest number of endpoints.
Sub-Rule Evaluation Order:
According to the documentation:
'Endpoints are inspected against each sub-rule in the order listed. When an endpoint matches a sub-rule, subsequent sub-rules are not evaluated for that endpoint.'
This sequential evaluation means that sub-rule order is critical to policy behavior.
Best Practice - Specific to General:
According to the guidelines:
The correct approach is to order sub-rules frommost specific to least specific:
First Sub-Rules (Most Specific)- Should capture thelowest number of endpoints
Very specific criteria
Narrow scope
Handles edge cases and special conditions
Middle Sub-Rules- Broader criteria
More endpoints matched
General conditions
Last Sub-Rule (Most General)- Catch-all sub-rule
Lowest specificity
Highest number of endpoints
Handles remaining unmatched endpoints
Why Specific Rules First:
According to the documentation:
'When an endpoint is found to match a sub-rule, no subsequent rules are evaluated for the endpoint.'
This 'first match wins' behavior requires:
Most specific rules first- Ensure special cases are handled correctly
General rules last- Catch remaining endpoints that don't match specific criteria
Avoid premature matches- If a general rule appears first, specific rules never execute
Example Sub-Rule Ordering:
According to the RADIUS documentation:
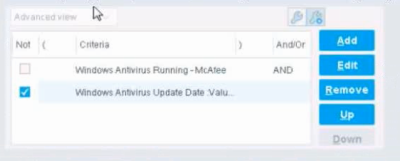
text
Sub-Rule 1 (Most Specific, Lowest Count):
Condition: Windows 7 AND Antivirus NOT Running AND Not Encrypted
Lowest number of endpoints - specific conditions
Sub-Rule 2 (More General, Moderate Count):
Condition: Windows Endpoint AND Missing Patches
More endpoints - broader criteria
Sub-Rule 3 (Least Specific, Highest Count - Catch-All):
Condition: Windows Endpoint (Any)
Highest number - captures all remaining Windows endpoints
Why Other Options Are Incorrect:
A . Last rule should capture the highest number- While the last rule may capture many endpoints, the key best practice is about the FIRST rule capturing the LOWEST
C . Second rule should capture the highest number- Sub-rule order is specific to general, not based on position 2
D . Last rule should not use a catch-all- Best practice is that the LAST rule should be the catch-all
E . First rule should capture the highest number- This is the OPPOSITE of correct practice
Referenced Documentation:
Forescout RADIUS Plugin Configuration Guide v4.3 - Sub-Rules section
Defining Forescout Platform Policy Sub-Rules
Sub-Rule Advanced Options