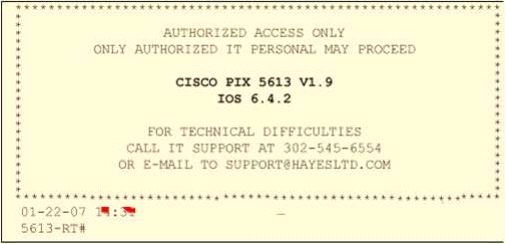
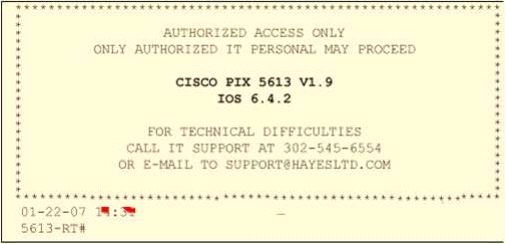
Paulette works for an IT security consulting company that is currently performing an audit for the firm ACEUnlimited. Paulette's duties include logging on to all the company's network equipment to ensure IOS versionsare up-to-date and all the other security settings are as stringent as possible.
Paulette presents the followingscreenshot to her boss so he can inform the clients about necessary changes need to be made. From thescreenshot, what changes should the client company make?
Exhibit:
Show Answer
Hide Answer