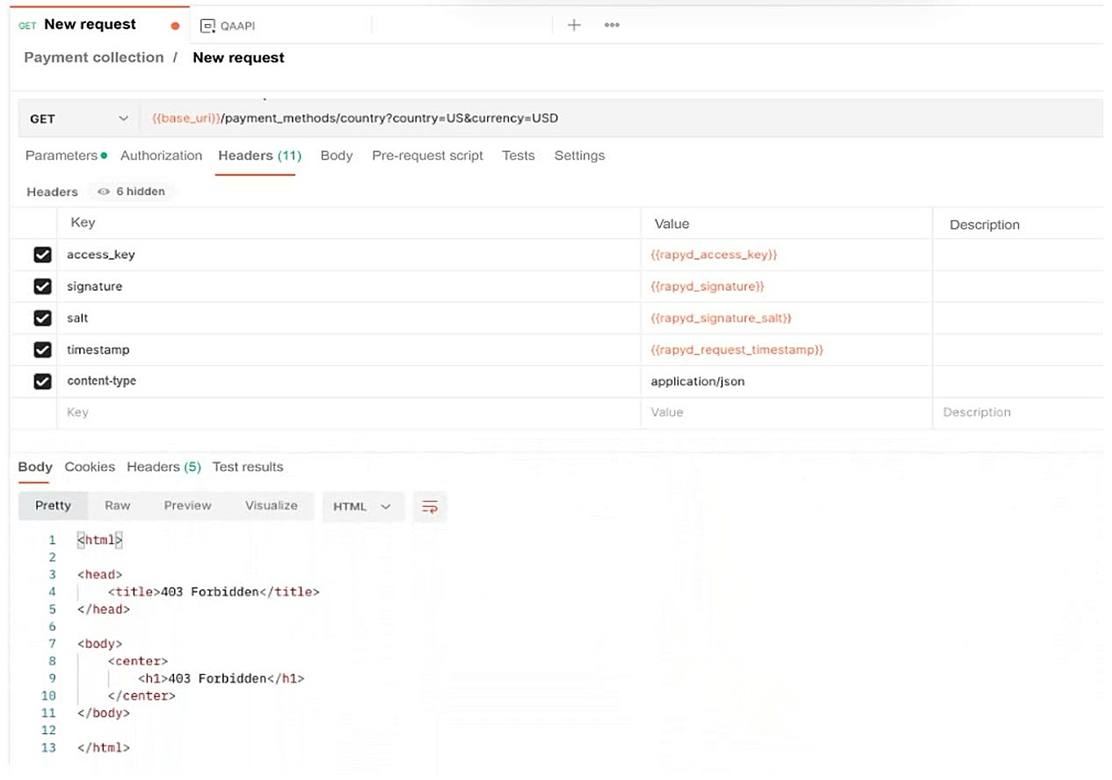
A developer reports errors when trying to access a web application. The developer uses Postman to troubleshoot and receives the following error:
Which of the following is the cause of the issue?
Show Answer
Hide Answer
Correct Answer:
B
The 403 Forbidden HTML response indicates the API is rejecting the call due to missing or invalid credentials (no valid access key/signature), not because of a missing resource (404), a networklevel block (you'd see a timeout or TCP reject), or an HTTP redirect. Proper authentication headers with a valid signature are required to avoid the 403 error.