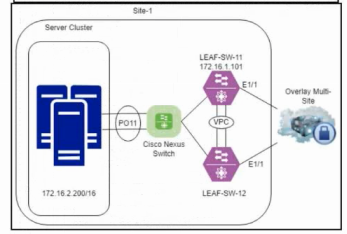
In a cloud-scale or data center--scale environment, Virtual Extensible LAN (VXLAN) is used as an overlay technology to transport Layer 2 segments over a Layer 3 underlay network. VXLAN encapsulates Layer 2 Ethernet frames inside UDP/IP packets, allowing broadcast, unknown unicast, and multicast (BUM) traffic and tenant Layer 2 domains to be extended across a routed IP fabric.
Key points aligned with Cisco Service Provider Cloud Infrastructure design principles:
VXLAN creates a Layer 2 overlay on top of a Layer 3 underlay.
The VXLAN Network Identifier (VNI) provides a much larger segmentation space than traditional VLANs, enabling multi-tenancy at cloud scale.
Because the underlay is pure Layer 3 (IP routed fabric), VXLAN allows you to interconnect Layer 2 segments between leaf switches or data centers over an IP/MPLS backbone without relying on large Layer 2 domains in the physical network.
Why the options evaluate as follows:
Option A: extends Layer 2 segments across the underlying Layer 3 infrastructure
This is the core benefit of VXLAN in cloud-scale designs. VXLAN encapsulates Layer 2 frames into IP/UDP headers, allowing isolated Layer 2 segments (per VNI) to be stretched across a routed IP network. This enables:
Multi-tenant Layer 2 connectivity across a distributed cloud fabric
Mobility of virtual machines or containers while keeping same IP/MAC addressing
Use of an IP-based leaf--spine or service provider underlay for scalability and resiliency
Option B: extends Layer 3 segments across the underlying Layer 2 infrastructure
This is the opposite of what VXLAN does. VXLAN is explicitly L2-over-L3, not L3-over-L2. Extending pure Layer 3 segments over Layer 2 is not the VXLAN use case.
Option C: reduces spanning-tree complexity across the Layer 2 infrastructure (Partially related but not the primary or direct benefit)
In modern designs, the underlay is Layer 3 routed, and VXLAN overlays provide logical Layer 2 segments. This design avoids dependence on spanning tree in the fabric, which indirectly reduces STP complexity. However, the fundamental, exam-relevant benefit is L2 extension over L3, so C is not the best or most accurate answer compared to A.
Option D: eliminates the need for a Layer 3 underlay in the service provider infrastructure
VXLAN absolutely requires an IP (Layer 3) underlay for transport. VXLAN tunnels are built over a routed infrastructure (leaf--spine, MPLS/IP core, etc.). It does not remove the need for Layer 3; it depends on it.