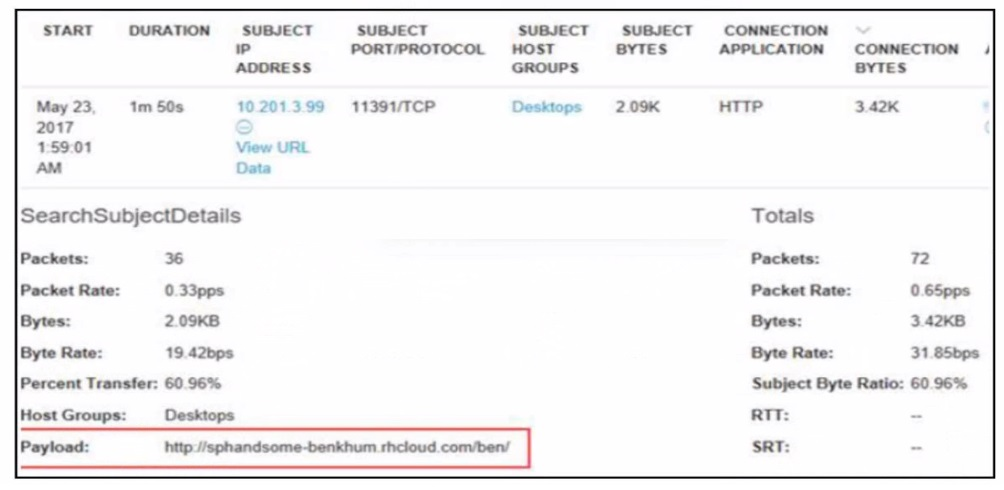
The correct answer is C. Host 10.201.3.99 is attempting to contact the C2 server to retrieve the payload.
Cisco Secure Network Analytics (Stealthwatch) detects Command-and-Control (C2) activity by analyzing network behavior, not by relying solely on known malicious indicators. In the exhibit, the critical investigative clue is the HTTP payload containing a suspicious external URL, which strongly suggests outbound communication from an internal host to an external command-and-control infrastructure.
The internal IP address 10.201.3.99 belongs to a workstation group (''Desktops''), indicating it is an internal endpoint, not a C2 server. This immediately rules out option B. Instead, the endpoint is acting as a compromised host (zombie) attempting to reach a remote server controlled by an attacker. This outbound beaconing behavior is a classic hallmark of C2 communication.
Option A is incorrect because packet count alone does not confirm C2 activity. C2 traffic is often low-and-slow, intentionally designed to blend in with normal traffic patterns. Option D is also incorrect because the payload does not describe the zombie endpoint; rather, it shows a remote URL, which is likely part of malware staging or command retrieval.
From a threat hunting and SOC perspective, the most valuable information is directionality and intent:
Internal host external suspicious domain
HTTP-based communication over an unusual port
Low data volume consistent with beaconing or payload retrieval
This aligns with MITRE ATT&CK -- Command and Control (TA0011) techniques such as Application Layer Protocols (T1071). Identifying which internal host is reaching out---and why---is essential for containment, endpoint isolation, and scope expansion.
Professionally, this insight enables the analyst to:
Quarantine host 10.201.3.99
Pivot to EDR telemetry on that endpoint
Block the external domain or IP
Hunt for similar beaconing patterns across the environment
In summary, the investigation is aided most by understanding that an internal host is actively communicating with a C2 server, making Option C the correct and operationally meaningful answer.